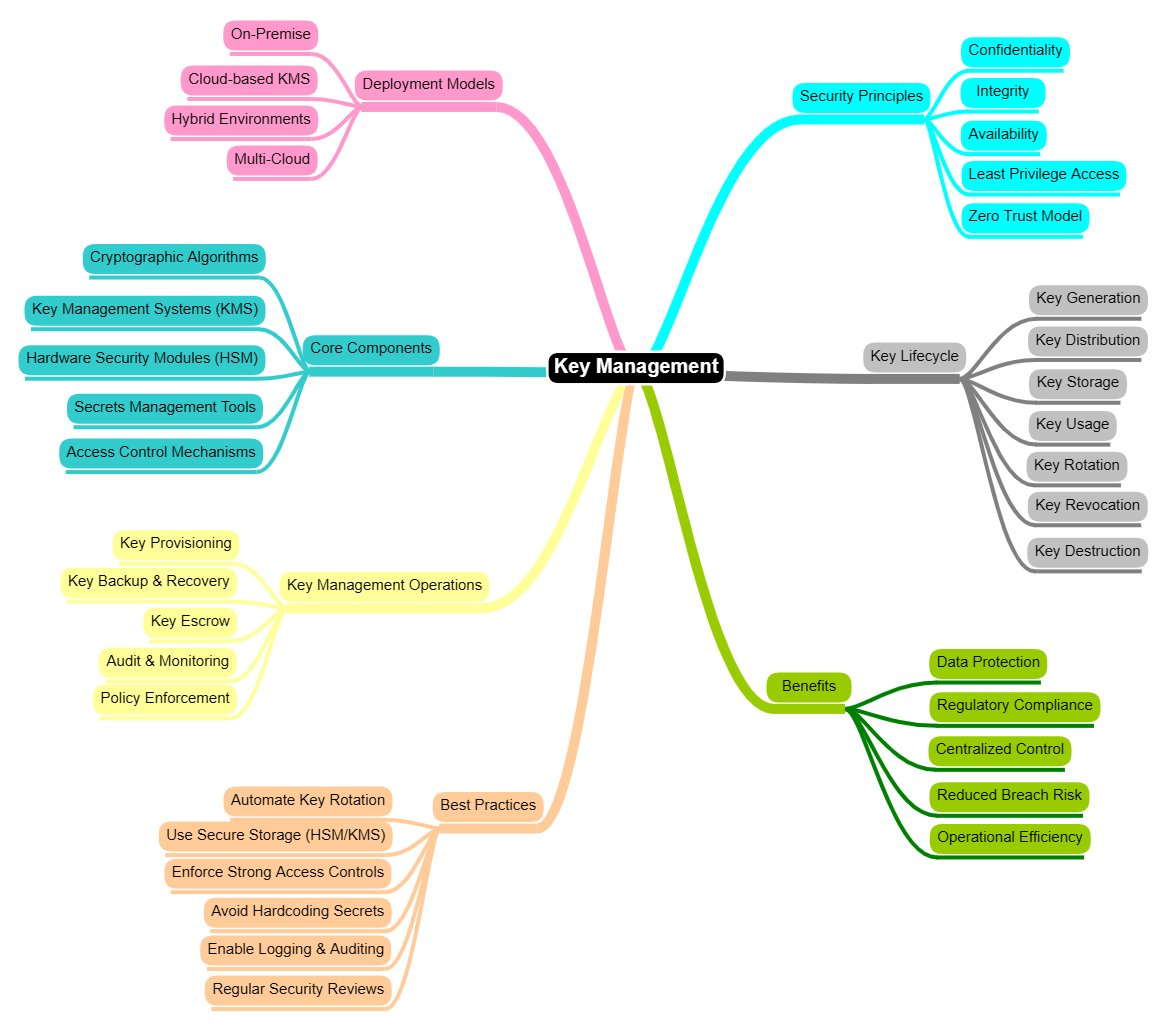
In my previous article, I explored the importance of managing SSL certificates and highlighted secure storage of private keys as a critical security control.
This control forms part of a broader process known as Key Management—a fundamental component of cybersecurity that ensures cryptographic keys are properly protected, managed, and governed throughout their lifecycle.
Why Key Management Matters
Encryption is only as strong as the protection of its keys. If keys are exposed, stolen, or mismanaged, attackers can easily decrypt sensitive data.
Key Management ensures:
- Confidentiality of data
- Integrity of information
- Secure access control
Core Components of Key Management
| Component | Role |
|---|---|
| Key Generation | Keys must be generated using strong cryptographic algorithms and secure random processes |
| Key Storage | Keys should be stored securely, often in:
|
| Key Distribution | Secure channels must be used to distribute keys to authorized systems and users |
| Key Rotation | Regularly updating keys reduces the risk of long-term exposure |
| Key Revocation | Compromised or unused keys must be revoked immediately to prevent misuse |
Benefits of Effective Key Management
| Benefit | How |
|---|---|
| Enhanced Data Security | Proper key management ensures that sensitive data remains encrypted and protected from unauthorized access |
| Regulatory Compliance | Organizations can meet compliance requirements such as:
|
| Reduced Risk of Data Breaches | Even if attackers gain access to encrypted data, they cannot decrypt it without the keys |
| Centralized Control | Key management systems provide a centralized way to control and monitor all cryptographic keys |
| Improved Operational Efficiency | Automation of key lifecycle processes reduces manual errors and administrative overhead |
| Scalability in Cloud Environments | Modern key management solutions integrate seamlessly with cloud platforms, supporting dynamic and scalable architectures |
Key Management in Modern Architectures
With the rise of:
- Microservices
- APIs
- Cloud-native applications
Key management has evolved to support distributed environments. Organizations now adopt:
- Cloud Key Management Services (KMS)
- Secrets management tools
- Zero Trust security models
This ensures that keys are securely managed across multiple services and environments.
TechE2E
A diverse group of technologists—ranging from beginners to experienced professionals—sharing insights, simplifying complex tech topics, and fostering meaningful discussions for readers at all stages of their journey.





